Introduction
Since 11 September 2001, there has been a global increase in AML/CTF[1] regulations relating to money remitters, both formal affiliated members of large global networks and unaffiliated operators connected via informal channels. These measures are designed to ensure that money remitters are bound by the AML/CTF regulations that other reporting entities have to comply with.
In Australia, money remitters are subject to the provisions of the Anti-Money Laundering & Counter Terrorism Financing Act 2006 (“AML/CTF Act”) and related rules. Progress in ensuring compliance by money remitters with the AML/CTF Act is progressing, but there is still much more work to be done. Both in Australia and in other jurisdictions. But increasingly, money remitters in Australia are being targeted for investigation by law enforcement authorities for alleged money laundering. Including for activities undertaken by them during officially sanctioned transition periods designed to enable them to adjust their business model to comply with new customer due diligence and know your customer obligations under the AML/CTF Act.
But as the following case example will demonstrate[2], being in compliance with AML/CTF obligations is not enough to prevent being charged with money laundering. This paper will outline the circumstances to the case and propose several issues that reporting entities in Australia and elsewhere should be mindful of when dealing with customers who might represent a beneficial owner.
Ramy[3] was charged with money laundering for engaging in 3 remittance services as instructed by 3 customers. The prosecution alleged that Ramy had engaged in money laundering because he had provided a remittance service on the basis of a false customer name or customer anonymity. In this case, it was alleged the real customer in the remittance process was a person referred to as “F”. Ramy appeared before the District Court of Western Australia in November 2016 to answer the criminal charge. After almost 4 days of deliberation, the charge of money laundering against Ramy was dismissed by the court.
Background
Ramy was a manager and director of an Australian company ITS Pty Ltd (“ITS”) which conducted a remittance business in Perth. His father was also a director but he lived overseas. The company was registered as a provider of designated remittance services with AUSTRAC, the Australian Financial Intelligence Unit and Anti-Money Laundering regulator. The registration took effect in 2012.
ITS had a AML/CTF Program as required under the AML/CTF Act 2006. That internal policy limited the transfer of cash to no more than $50,000 per person per day. The policy also prescribed in Part B, the identification process to be followed for all new customers. The policy was clear, that all new customers would be identified in a face to face relationship.
ITS provided remittance services mainly to China and neighbouring countries. It also provided some foreign exchange services.
A person referred to here as “F” wanted to remit money from Australia and he asked “B” to arrange for other people to undertake the remittances. B was a foreign student studying in Australia and earned some money driving people around Perth which included F. Prior to this occasion, F and B had sent money from Australia and had been previous customers of ITS. Both men were known to Ramy as past customers of ITS.
As instructed, B recruited three backpackers in Australia to remit money. Each person was engaged to remit $50,000. In relation to the current circumstances, the remittance process commenced with B driving to F’s house and collecting him and the cash. B was often engaged by F as a driver. F provided to B on a piece of paper the numbers for the accounts held in China which were to receive the money to be remitted from Australia. Both men then drove to the premises of ITS in Perth.
On arrival, B took the money into the premises of ITS and gave it to Ramy who counted it. B also provided Ramy with the Chinese account numbers. While at the premises B contacted three backpackers, “X”, “Y” and “Z”. Sometime later, they arrived to remit the money. In response to questions from Ramy and in accordance with the customer identification policy of ITS, each person presented their passports to Ramy for identification and provided their telephone numbers and addresses in Perth. Ramy scanned the front page of each document, capturing a facial image in colour of each customer. The front page including the photograph together with transactional information were retained on record in a customer file, in accordance with AML/CTF policy of ITS.
For each remittance, being $50,000 cash in each case, Ramy prepared a receipt recording the name of each person and the account details of where the money was to be sent, namely to China. All of the backpackers then signed the receipt acknowledging that the details were true. That receipt or remittance form as referred to by the court, contained the reference number for the transaction, the date of the transaction, the name of the person sending the money, the currency received, the amount received, the transfer fee of $10, the exchange rate being offered, the currency in which the transfer was to be paid, the amount in that currency to be paid and the beneficiary account to receive the funds. But importantly, the document contained a declaration which was acknowledged by each backpacker signing the form stating that:
“I confirm that all information I have provided is accurate and I understand relevant requirements of AUSTRAC under Australian law. I declare this money remittance service is not used for any illegal purpose and the funds are from legitimate sources. The information provided is in accordance with the regulations for the prevention of money laundering, terrorist financing and illegal activities”.
After completing the identification process and signing the receipt, the backpackers departed the premises where they were each paid $100 by B. At all times the process was overseen by B, who was also paid around $200 to $400 by F for his services to him, including his taxi driving services.
Ramy then arranged for the money to be deposited into the Chinese accounts as instructed.
There was no information or suggestion put to the court by the prosecution that the identifying information provided by the three backpackers was not entirely genuine. Each person, referred to as X,Y and Z, gave their real names, used genuine passports, real addresses and real telephone numbers.
The Money Laundering Offence
Australia has an extensive money laundering offence framework that is little understood or known by reporting entities. The Commonwealth Criminal Code, Australia’s primary national criminal offence legislation, contains 38 money laundering offences. Of those offences, one offence contained in Section 400.9 of the code is relevant. Section 400.9 contains an offence that relates to the dealing of money or property that is of $100,00 or more. This offence is not the most serious money laundering offence in Australia, providing a penalty on conviction of imprisonment for a maximum of 3 years. But it can be effective in combating money laundering if applied in appropriate circumstances. And a serious violation of a person’s rights if it is not.
Two features of the Section 400.9 offence that makes it a significant legislative weapon, is the minimal requirement of establishing the source of funds are proceeds of crime on the basis of reasonable suspicion only. And secondly, there is no requirement for the prosecution to establish the mental state of the accused person at the time they dealt with the money or property. Any knowledge they held, if any, as to the source of the funds is irrelevant in determining guilt or innocence. The impact of this provision, as will be seen in this case, is that a person not involved in the predicate crime and having no knowledge of the source of the funds or any suspicion as to the source of the funds that would require him or her to report it as a suspicious matter, could be convicted of money laundering.
Ramy was charged with an offence against Section 400.9 in that he dealt with money in which it was reasonable to suspect that the money (in this case more than $100,000) was proceeds of crime.
The prosecution can prove reasonable suspicion by either demonstrating by direct or circumstantial evidence or both, the grounds that a reasonable suspicion exists in relation to any money or property. Or the prosecution can rely on what are known as the “deeming provisions” of Section 400.9 to establish reasonable suspicion. In the case involving Ramy, the prosecution decided to apply the latter.
The deeming provisions are extensive and beyond the scope of discussion in this paper. Most of the provisions involve proving the commission of another offence contained in the AML/CFT Act 2006, which is then used to satisfy the reasonable suspicion. By proving that other offence, the reasonable suspicion is deemed to be proven. The prosecution does not have to identify any other offence as being the source of the funds.
For the purposes of Ramy’s case, the prosecution relied upon establishing that his company, had committed an offence against Section 139 of the AML/CTF Act 2006. If an offence against section 139 could be proven, then it is taken to be proved that it was reasonable to suspect that the money was the proceeds of crime.
A person commits an offence pursuant to section 139 AML/CTF Act 2006, if the person is a reporting entity (in this case a money remitter but applies to all reporting entities including a bank) and the person commences to provide a designated service (in this case, a remittance service) and the person does so using a false customer name or the person does so on the basis of customer anonymity and at least one provision of division 2, 3 or 4 of Part 2 (which relate to identification procedures) of the AML/CTF Act applies to the provision of the designated service. The provision of one aspect of Part 2 was not an issue for the court to content with, as Ramy undertook an identification procedure for each backpacker in accordance with Australian AML/CTF legislation and the AML/CTF Program of ITS.
Source of the Funds
Ramy conducted three international funds transfers (remittances) in the names of X, Y and Z, with each transaction being $50,000. Under Australian money laundering law, the prosecution can combine the three transactions into one criminal charge. Which means that Ramy was charged with the more serious of the section 400.9 provisions, dealing with money amounting to over $100,000, reasonably suspected of being the proceeds of crime.
X, Y and Z were not the source of the money. They had been contracted by B to help him remit the funds. B was also not the source of the funds.
The source of the funds was F, who at the time the remittance processes were being processed, remained in a vehicle outside the premises occupied by ITS.
Ramy was never informed about the source of the funds by any person. But he had ensured that each backpacker had signed a declaration confirming that the money was not derived from crime or intended to be used in crime.
Court Finding
When the prosecution had finished delivering its case, the defence lodged an application pursuant to section 108 of the Criminal Procedure Act (WA) that Ramy had no case to answer. This is an application that is lodged prior to the defence tendering its evidence before the court to rebut the prosecution case. The court accepted the defence submission and dismissed the prosecution case negating any need for the defence to respond further.
In dismissing the case, the court accepted the arguments put before it by the defence:
· Section 6 of the AML/CTF Act 2006 defines who is to be the subject of the customer identification procedure, and in relation to remittances, it is the person from whom an instruction is accepted for the transfer of money. It is not the person who gives an instruction.
· A false customer name means a name other than a name by which the customer is commonly known. Customer anonymity is not defined in the AML/CTF Act and therefore recourse must be had to the meaning of the word anonymous which means nameless or of unknown name. The AML/CTF Act 2006 specifies who the customer is for any particular designated service. Item 31 of Section 6 of that act specifies that in relation to a remittance arrangement, the customer is the person from whom an instruction is accepted for the transfer of money.
· If the customer in each transaction was X, Y and Z, then Ramy did not provide the designated service using a false customer name or alternatively did not provide it on the basis of customer anonymity. The customer is not to be equated with the source of the money or the owner of the money or the person on whose behalf the money was remitted. In this case, in relation to the last two points, it was F[4].
· The mere provision of bank details did not amount to the instruction to remit funds. They were incorporated into the instruction to remit money once it was received. That instruction was not received from B. He contracted X, Y and Z and assisted them on their arrival. If they had not arrived, then the transactions would not have occurred. B had no intention of remitting the money. And ITS would not have been able to comply with its own customer identification procedures until they did arrive, which it is required to do before engaging in a remittance service.
· There is no requirement for an instruction to a remitter to be in writing. But how the instruction is given is not relevant. It is the acceptance by the remitter that binds the arrangement (the court mentioned that the remitter merely offers a service involving the remittance of money at various rates and commission. This amounts to an “invitation to treat”[5].
· The AML/CTF Act does not specify the owner of money, the source of the money, or on whose behalf the money is remitted. Australian law focuses on the person from whom an instruction is accepted.
The court held that the prosecution could not prove that ITS committed an offence pursuant to section 139 and therefore was unable to prove the second element of the offence charged pursuant to section 400.9. Based on the above arguments, no properly instructed jury, acting reasonably, could find that ITS had accepted an instruction from F to transfer funds. In relation to the receipt of the bank account information from B, the court held the view that it was only information received by Ramy in anticipation of receipt of the instructions from the backpackers.
Relevance to Reporting & Non-Reporting Entities
This case has several issues that should be of concern for all reporting entities, large and small. And not just for money remitters.
The two prime issues are understanding the beneficial owner and Australia’s money laundering laws making criminals out of innocent people.
Under FATF Standards and Australian AML/CTF law, a reporting entity is required to identify all and any beneficial owner behind a transaction or an account. And while that sounds reasonable, it is an extremely difficult process to undertake in practice. Often a beneficial owner is hidden behind a corporate entity or a third party. And while X, Y and Z were the transferrers of funds in Ramy’s case, the potential real owner and therefore beneficial owner, noting that it was not established, was F. He was not present when the transactions took place. The question therefore is if a reporting entity is required to identify the beneficial owner of funds or an account or transaction, how can they do that when that person is masked by remaining outside of the premises? How far should the reporting entity go? Place camera’s outside their premises to identify other parties? Record all car registrations in the vicinity? Obviously both solutions would not be practical or effective to implement. And given that under Australia law, a transferrer of funds is the person who actually communicates an instruction to a reporting entity, namely a remitter, what is the point in establishing the beneficial owner anyway?
“…..a reporting entity is required to identify all and any beneficial owner behind a transaction or an account. And while that sounds reasonable, it is an extremely difficult process to undertake in practice”
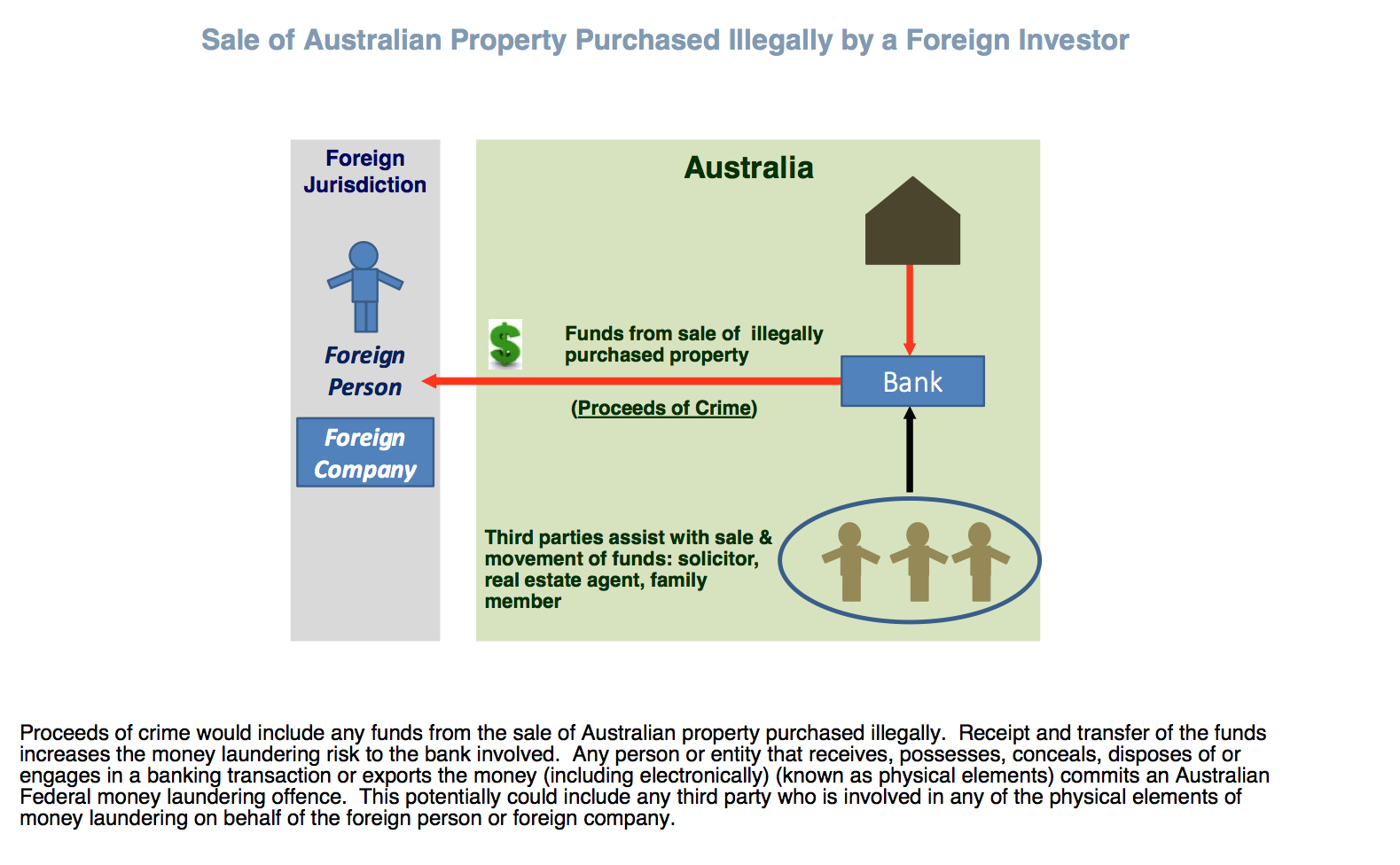
In regards to Australian money laundering law, it is beyond the scope of this paper to explain in full the Commonwealth provisions. But all entities should note the wide reach of Section 400.9. A person can be convicted of money laundering on establishment of “reasonable suspicion” that money or property they deal with, is the proceeds of crime.
ITS had in place an AML/CTF Program containing both Part A and Part B that was a risk based assessment prepared in compliance with the AML/CTF Act. If Ramy had acted, and it appears he did, in accordance with the AML/CTF program developed for GF, how was it that he was charged with money laundering? What risks did the business fail to identify?
A risk based approach to combating money laundering pushes the onus from AUSTRAC (or any financial intelligence unit) onto the reporting entity. And it is often misunderstood what is meant by a risk based approach. RBA does not mean there will be “zero faults”. RBA is not designed to guarantee absolute assurance that all money laundering risks will be identified, prevented and/or reported. It is only designed to give “reasonable assurance”. When a risk based approach is implemented for anything, it means and does result in the system failing at times. And failure must be accepted, particularly in relation to money laundering, because that crime often involves deception, which is masked in documents and by people in what they do or don’t do or say or don’t say. In money laundering things and people lie. And while not their sole purpose, money laundering techniques can defeat AML/CTF controls. Any control can be defeated by them. This is not often understood by reporting entities, by AUSTRAC (and other financial intelligence units) and by investigative agencies such as police.
“RBA does not mean there will be “zero faults”. RBA is not designed to guarantee absolute assurance that all money laundering risks will be identified, prevented and/or reported. It is only designed to give reasonable assurance”.
Therefore, when a control fails, is it appropriate to charge an employee of the reporting entity involved, in this case Ramy with money laundering? If the answer is yes, then Australia can expect a large number of people to be charged with money laundering as AML/CTF controls fail every day and fail often.
And this could occur in relation to the Section 400.9 offences, because as reported in this case, the prosecution needs only to prove that there is reasonable suspicion the money is proceeds of crime. Knowledge by the accused at the time they dealt with the money or property is irrelevant. However, an accused person charged with Section 400.9 has a defence. If they can establish that they had no reasonable grounds to suspect the money or property, as the case may be, was not derived from any unlawful activity, then they are entitled to be acquitted. But unlawful activity includes both minor and serious offences. Including offences against Australian law (Commonwealth, State and Territory) and foreign law.
Getting back to Ramy’s case. How is a money remitter, or an employee of any reporting entity, including AML monitoring staff in a bank (and for that matter a non-reporting entity in Australia for example a real estate firm) expected to know the criminal law of every Australian jurisdiction and every foreign country? For example, how are staff of a reporting entity, particularly a small money remitter, expected to know the offences contained in the Primary Produce Safety (Egg) Regulations 2014 of Tasmania? Namely, supplying any egg, or egg product, that has not been lawfully produced for human consumption. Or offences relating to the unlawful dealing in precious stones in Botswana?
Given Australia’s ethnic diversity, it is expected that a money remitter would be involved directly or indirectly in sending or receiving funds around the world. And it would therefore be highly probable that they would handle money that could be the proceeds of crime being sent from Australia or received from overseas. They cannot be expected to make an accurate assessment on whether every transaction they are involved in, is reasonably suspected of being the proceeds of crime on every single occasion. A RBA approach to money laundering will not ensure that they can. But in Australia, if they don’t and the transaction is detected by the authorities and they hold the view there is reasonable suspicion that the money is proceeds of crime, they face the prospect of being charged with money laundering. The criminal money laundering laws in Australia are therefore inconsistent with and clash with the risk based approach adopted in anti-money laundering frameworks. RBA might identify the risks that a firm or a person might handle the proceeds of crime and assist in the activity being reported to AUSTRAC, but it offers no protection to the staff of a reporting entity from being charged with money laundering, if not suspicion matter report is filed.
“The criminal money laundering laws in Australia are therefore inconsistent with and clash with the risk based approach adopted in anti-money laundering frameworks”
Recommendations
Like any business risk, money laundering risk needs to be mitigated. Being charged with money laundering can destroy or damage a business. Therefore, prosecution risk and reputational risk need to be mitigated as well. These risks need to be captured in the risk management plan or AML/CTF program of reporting entities. And steps taken to mitigate against them to the extent possible. But planning to reduce the risk of inappropriate action by an FIU or law enforcement agency is an extremely difficult task, if not an impossible task, with the consequences for an employee of a reporting entity and the entity itself being severe.
Taking into consideration the issues raised in this case, reporting entities, should consider adopting the following practices:
1. Risk indicators in AML/CTF risk plans should incorporate foreign students and foreign travellers as a risk.
2. In relation to foreign customers, reporting entities should demand proof of residence. Are they in the country legally? Is their given address accurate? (via Google check).
3. Ask themselves the question, why is a foreign student or traveller sending a large amount of money offshore? Or receiving a large amount of money onshore? Or regularly sending smaller amounts offshore which in total amount to a large amount of money for their status and or age?
4. Train staff to make an assessment on whether any money or property involved in a transaction is reasonably suspected of being the proceeds of crime. If it is, report it as a suspicious matter. And if in doubt, err on the side of caution and report it to AUSTRAC (or other FIU if offshore) anyway. This might lead to over reporting and a rebuke received from AUSTRAC. But it is not AUSTRAC that faces the risk of prosecution for money laundering. It is the entity and its employees. Any feedback from AUSTRAC to a reporting entity that it is “defensive reporting” should be ignored until the reporting entity has received legal advice from a lawyer or barrister who specialises in criminal money laundering law.
5. Staff should be trained in the Criminal money laundering law of Australia, particularly Commonwealth money laundering law.
6. AML/CTF programs should address the risks posed by the wide reach of Commonwealth money laundering law, particularly the fault of elements of knowledge, recklessness and negligence and the reasonable suspicion element and deeming provisions in Section 400.9 Criminal Code Act 1995.
7. Insert into any application to remit or receive funds the following statements in an attempt to identify the beneficial owner:
a. Q.1 Are the funds you are sending or receiving your money?
b. Q. 2 Have you been asked to act on behalf of another party to send the money or to receive the money?
If the answer to question 1 is no and/or the answer to question 2 yes, then further due diligence should be applied.
Malkara Consulting is able to provide guidance to any reporting entity on lawyers and/or barristers who have experience with prosecuting and defending Commonwealth money laundering cases.
____________________________________________________________________
AML advice in this case was provided by Malkara Consulting.
[1] Internationally referred to as AML/CFT.
[2] Details withheld to protect the identity and reputation of the business and all persons involved in the management of the business.
[3] Not the defendant’s real name. Changed to protect his identity.
[4]The prosecution argued that X, Y and Z were sham customers signing the remittance forms with the effect that F, achieved anonymity or was identified by a false name in that he was not known by their names.
[5] Similar to a retailer offering goods for sale. The customer accepts the offer by paying a consideration usually money. But in the case of a remitter it is the giving of an instruction which is accepted by the remitter that binds the contract.